Yes!! you heard it, The question which I will be talking about in this article is worth more than a trillion dollars, any who can crack it is able to get that money in seconds. Are you not interested in knowing what is this question about and trying to solve it, then let's get started.
Prerequisites For the Questions
What is Crypto Mining?
Let's get a good understanding of how mining works. The first thing to do for starting mining is to download a good miner which will mine your crypto that you specify and will basically take a lot of time to get a good amount of money from it, and if the coin is more populated it might even take an eternity to mine. So let's see what does mining software does. The Point to remember is that many popular crypto networks are built on SHA or Secure Hashing Algorithm, and the mining software which you use just implements and runs the SHA. But what is SHA?
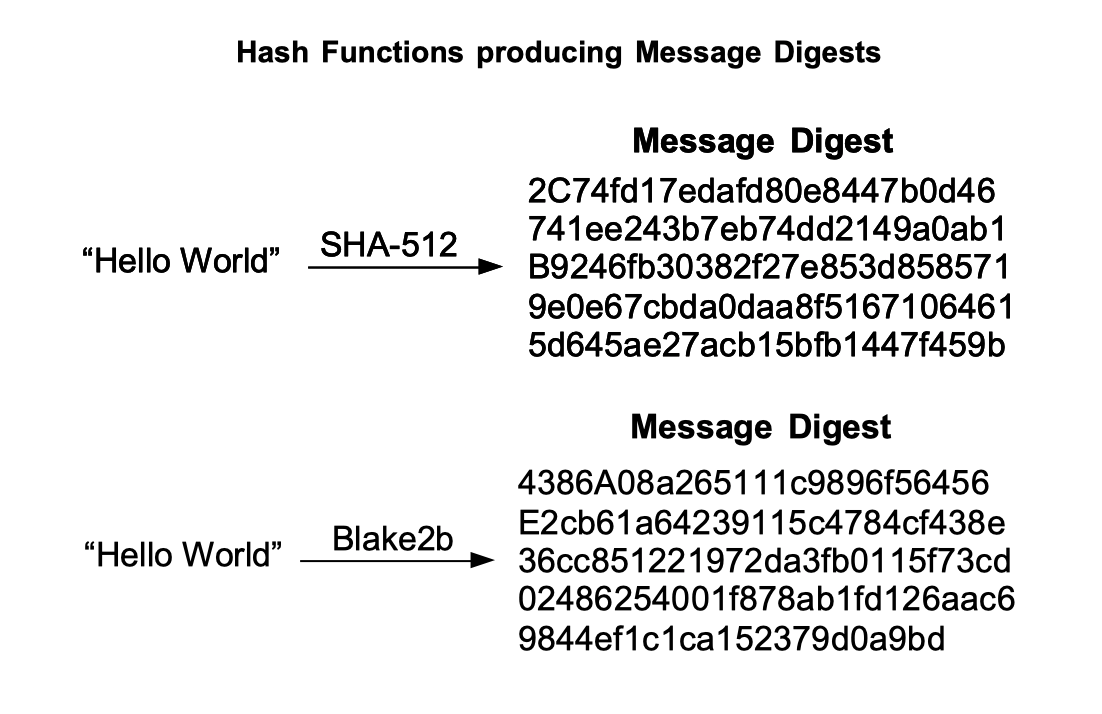
SHA is an Algorithm to convert any data in a constant number of a byte sequence. If you learned about cryptography you might even have a good knowledge of how a hashing algorithm works. For more details, let's consider an example. Suppose you have a file or a piece of information that is highly confidential and you want to transfer it to your friend on the network. But while transferring into the network what if some intruder interrupts and changes the content of it. We are losing the integrity of the data here. so there should be some parameters by which we can check the integrity of the information, thus hashing algorithms were introduced. Let's see how hashing algorithms ensure data integrity.
Let's consider the same case where you want to transfer information to your friend but apart from information you also transfer from additional information which is known as message-digest. A message digest is obtained when the information you want to send is given as an input to the hashing algorithm. The user at the other end again computes the hash of the message and compares it with the hash of the sender, if both matches then there is no alteration made in the data, or else someone changed the information.
But Why Are We Talking About SHA?
The underlying infrastructure of bitcoin and many other cryptocurrencies are made of SHA-256 and SHA-512, when you do mining your computer hardware runs the SHA algorithm, if we are specifically speaking about Bitcoin then it is SHA-256, there are also some other steps involved in this but we just need the hashing part for today's question. When you get a job from the pool you need to find a hash which is n no of 0's and this is done by just guessing the inputs and trying all possibilities if you find the sequence then you just mined your first bitcoin or any other crypto. But hold your horses there, this task is not that easy as it looks, There are literally so many combinations of the inputs for the SHA the number is 2^256 which is more than the no of atoms in the whole universe, that's how complicated it is. Literally, thousands of people mine every day and earn bitcoins. I have covered the profitability of mining in 2021 visit here for more information.
Here comes the Billion Dollar Question.
So we talked about hash but as we are talking about it did anyone of you thought of implementing the SHA algorithm more efficiently, Yes you guessed it, If you find some way to implement the SHA algorithm more efficiently, fastly and computational feasible then you might mine faster than the entire world. and get billion dollars worth of bitcoins every day.
Not only mining the Entire Blockchain is made of Hashing functions, if you find some way to get collision in the algorithm then you will be the next richest person in the world. Since the first publication of the SHA algorithm, there are no collisions detected till now, but wait what are collisions. Collisions are nothing but two different inputs of the hash function yielding the same digest. Suppose we get the digest and are able to find the string which can cause the collision then it is easy to interrupt any data flow and do alterations in it. Many Cryptaaalyst is yet trying to find collisions in the SHA algorithm but there is not much progress in it.
So are you also interested in Cracking this Algorithm? Comment in this comment section about your thoughts.